Table of Contents
Samba-3 implements a new capability to work concurrently with multiple account backends. The possible new combinations of password backends allows Samba-3 a degree of flexibility and scalability that previously could be achieved only with MS Windows Active Directory. This chapter describes the new functionality and how to get the most out of it.
Samba-3 provides for complete backward compatibility with Samba-2.2.x functionality as follows:
- Plain Text
This isn't really a backend at all, but is listed here for simplicity. Samba can be configured to pass plaintext authentication requests to the traditional UNIX/Linux
/etc/passwdand/etc/shadowstyle subsystems. On systems that have Pluggable Authentication Modules (PAM) support, all PAM modules are supported. The behavior is just as it was with Samba-2.2.x, and the protocol limitations imposed by MS Windows clients apply likewise. Please refer to Technical Information for more information regarding the limitations of Plain Text password usage.- smbpasswd
This option allows continued use of the
smbpasswdfile that maintains a plain ASCII (text) layout that includes the MS Windows LanMan and NT encrypted passwords as well as a field that stores some account information. This form of password backend does not store any of the MS Windows NT/200x SAM (Security Account Manager) information required to provide the extended controls that are needed for more comprehensive inter-operation with MS Windows NT4/200x servers.This backend should be used only for backward compatibility with older versions of Samba. It may be deprecated in future releases.
- ldapsam_compat (Samba-2.2 LDAP Compatibility)
There is a password backend option that allows continued operation with an existing OpenLDAP backend that uses the Samba-2.2.x LDAP schema extension. This option is provided primarily as a migration tool, although there is no reason to force migration at this time. This tool will eventually be deprecated.
Samba-3 introduces a number of new password backend capabilities.
- tdbsam
This backend provides a rich database backend for local servers. This backend is not suitable for multiple Domain Controllers (i.e., PDC + one or more BDC) installations.
The tdbsam password backend stores the old smbpasswd information plus the extended MS Windows NT / 200x SAM information into a binary format TDB (trivial database) file. The inclusion of the extended information makes it possible for Samba-3 to implement the same account and system access controls that are possible with MS Windows NT4/200x-based systems.
The inclusion of the tdbsam capability is a direct response to user requests to allow simple site operation without the overhead of the complexities of running OpenLDAP. It is recommended to use this only for sites that have fewer than 250 users. For larger sites or implementations, the use of OpenLDAP or of Active Directory integration is strongly recommended.
- ldapsam
This provides a rich directory backend for distributed account installation.
Samba-3 has a new and extended LDAP implementation that requires configuration of OpenLDAP with a new format Samba schema. The new format schema file is included in the
examples/LDAPdirectory of the Samba distribution.The new LDAP implementation significantly expands the control abilities that were possible with prior versions of Samba. It is now possible to specify “per user” profile settings, home directories, account access controls, and much more. Corporate sites will see that the Samba Team has listened to their requests both for capability and to allow greater scalability.
- mysqlsam (MySQL based backend)
It is expected that the MySQL-based SAM will be very popular in some corners. This database backend will be of considerable interest to sites that want to leverage existing MySQL technology.
- pgsqlsam (PostGreSQL based backend)
Stores user information in a PostgreSQL database. This backend is largely undocumented at the moment, though it's configuration is very similar to that of the mysqlsam backend.
- xmlsam (XML based datafile)
Allows the account and password data to be stored in an XML format data file. This backend cannot be used for normal operation, it can only be used in conjunction with pdbedit's pdb2pdb functionality. The DTD that is used might be subject to changes in the future.
The
xmlsamoption can be useful for account migration between database backends or backups. Use of this tool will allow the data to be edited before migration into another backend format.
Old Windows clients send plain text passwords over the wire. Samba can check these passwords by encrypting them and comparing them to the hash stored in the UNIX user database.
Newer Windows clients send encrypted passwords (so-called LanMan and NT hashes) over the wire, instead of plain text passwords. The newest clients will send only encrypted passwords and refuse to send plain text passwords, unless their registry is tweaked.
These passwords can't be converted to UNIX-style encrypted passwords. Because of that, you can't use the standard UNIX user database, and you have to store the LanMan and NT hashes somewhere else.
In addition to differently encrypted passwords, Windows also stores certain data for each
user that is not stored in a UNIX user database. For example, workstations the user may logon from,
the location where the user's profile is stored, and so on. Samba retrieves and stores this
information using a passdb backend. Commonly available backends are LDAP, plain text
file, and MySQL. For more information, see the man page for smb.conf regarding the
passdb backend parameter.
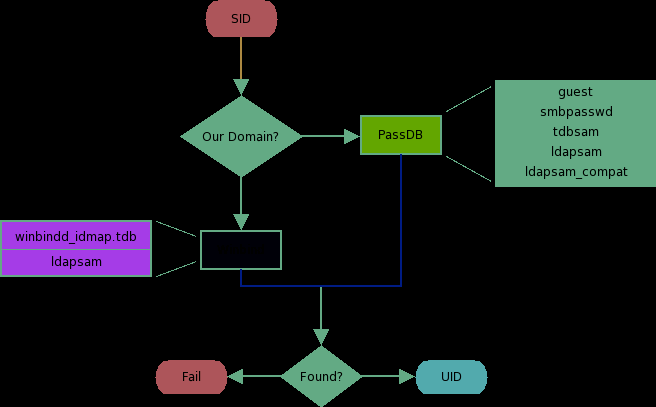
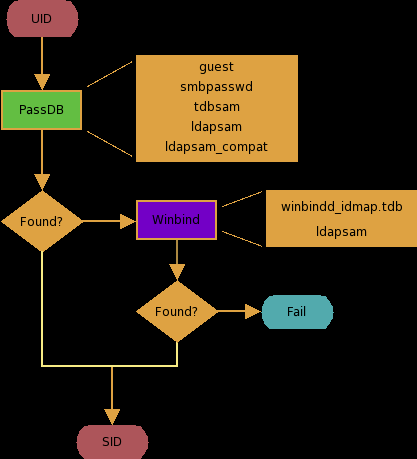
The resolution of SIDs to UIDs is fundamental to correct operation of Samba. In both cases shown, if winbindd is not running, or cannot be contacted, then only local SID/UID resolution is possible. See resolution of SIDs to UIDs and resolution of UIDs to SIDs diagrams.
The UNIX and SMB password encryption techniques seem similar on the surface. This similarity is, however, only skin deep. The UNIX scheme typically sends clear-text passwords over the network when logging in. This is bad. The SMB encryption scheme never sends the clear-text password over the network but it does store the 16 byte hashed values on disk. This is also bad. Why? Because the 16 byte hashed values are a “password equivalent.” You cannot derive the user's password from them, but they could potentially be used in a modified client to gain access to a server. This would require considerable technical knowledge on behalf of the attacker but is perfectly possible. You should thus treat the data stored in whatever passdb backend you use (smbpasswd file, LDAP, MYSQL) as though it contained the clear-text passwords of all your users. Its contents must be kept secret and the file should be protected accordingly.
Ideally, we would like a password scheme that involves neither plain text passwords on the network nor on disk. Unfortunately, this is not available as Samba is stuck with having to be compatible with other SMB systems (Windows NT, Windows for Workgroups, Windows 9x/Me).
Windows NT 4.0 Service Pack 3 changed the default setting so plaintext passwords are disabled from being sent over the wire. This mandates either the use of encrypted password support or editing the Windows NT registry to re-enable plaintext passwords.
The following versions of Microsoft Windows do not support full domain security protocols, although they may log onto a domain environment:
MS DOS Network client 3.0 with the basic network redirector installed.
Windows 95 with the network redirector update installed.
Windows 98 [Second Edition].
Windows Me.
Note
MS Windows XP Home does not have facilities to become a Domain Member and it cannot participate in domain logons.
The following versions of MS Windows fully support domain security protocols.
Windows NT 3.5x.
Windows NT 4.0.
Windows 2000 Professional.
Windows 200x Server/Advanced Server.
Windows XP Professional.
All current releases of Microsoft SMB/CIFS clients support authentication via the SMB Challenge/Response mechanism described here. Enabling clear-text authentication does not disable the ability of the client to participate in encrypted authentication. Instead, it allows the client to negotiate either plain text or encrypted password handling.
MS Windows clients will cache the encrypted password alone. Where plain text passwords are re-enabled through the appropriate registry change, the plain text password is never cached. This means that in the event that a network connections should become disconnected (broken), only the cached (encrypted) password will be sent to the resource server to effect an auto-reconnect. If the resource server does not support encrypted passwords the auto-reconnect will fail. Use of encrypted passwords is strongly advised.
Plaintext passwords are not passed across the network. Someone using a network sniffer cannot just record passwords going to the SMB server.
Plaintext passwords are not stored anywhere in memory or on disk.
Windows NT does not like talking to a server that does not support encrypted passwords. It will refuse to browse the server if the server is also in User Level security mode. It will insist on prompting the user for the password on each connection, which is very annoying. The only things you can do to stop this is to use SMB encryption.
Encrypted password support allows automatic share (resource) reconnects.
Encrypted passwords are essential for PDC/BDC operation.
Plaintext passwords are not kept on disk, and are not cached in memory.
Uses same password file as other UNIX services such as Login and FTP.
Use of other services (such as Telnet and FTP) that send plain text passwords over the network, so sending them for SMB is not such a big deal.
Every operation in UNIX/Linux requires a user identifier (UID), just as in MS Windows NT4/200x this requires a Security Identifier (SID). Samba provides two means for mapping an MS Windows user to a UNIX/Linux UID.
First, all Samba SAM (Security Account Manager database) accounts require a UNIX/Linux UID that the account will map to. As users are added to the account information database, Samba will call the add user script interface to add the account to the Samba host OS. In essence all accounts in the local SAM require a local user account.
The second way to effect Windows SID to UNIX UID mapping is via the
idmap uid and idmap gid parameters in smb.conf.
Please refer to the man page for information about these parameters.
These parameters are essential when mapping users from a remote SAM server.
Samba-3 has a special facility that makes it possible to maintain identical UIDs and GIDs on all servers in a distributed network. A distributed network is one where there exists a PDC, one or more BDCs and/or one or more Domain Member servers. Why is this important? This is important if files are being shared over more than one protocol (e.g., NFS) and where users are copying files across UNIX/Linux systems using tools such as rsync.
The special facility is enabled using a parameter called idmap backend.
The default setting for this parameter is an empty string. Technically it is possible to use
an LDAP based idmap backend for UIDs and GIDs, but it makes most sense when this is done for
network configurations that also use LDAP for the SAM backend. Following
example shows that.
Example 10.1. Example configuration with the LDAP idmap backend
[global] |
idmap backend = ldap:ldap://ldap-server.quenya.org:636 |
| # Alternately, this could be specified as: |
idmap backend = ldap:ldaps://ldap-server.quenya.org |
A network administrator who wants to make significant use of LDAP backends will sooner or later be exposed to the excellent work done by PADL Software. PADL http://www.padl.com have produced and released to open source an array of tools that might be of interest. These tools include:
nss_ldap: An LDAP Name Service Switch module to provide native name service support for AIX, Linux, Solaris, and other operating systems. This tool can be used for centralized storage and retrieval of UIDs/GIDs.
pam_ldap: A PAM module that provides LDAP integration for UNIX/Linux system access authentication.
idmap_ad: An IDMAP backend that supports the Microsoft Services for UNIX RFC 2307 schema available from the PADL web site.
Samba doesn't provide a turnkey solution to LDAP. It is best to deal with the design and configuration of an LDAP directory prior to integration with Samba. A working knowledge of LDAP makes Samba integration easy and the lack of a working knowledge of LDAP can make it one a frustrating experience.
Computer (machine) accounts can be placed where ever you like in an LDAP directory subject to some constraints that are described in this chapter.
The POSIX and SambaSAMAccount components of computer (machine) accounts are both used by Samba. i.e.: Machine accounts are treated inside Samba in the same way that Windows NT4/200X treats them. A user account and a machine account are indistinquishable from each other, except that the machine account ends in a '$' character, as do trust accounts.
The need for Windows user, group, machine, trust, etc. accounts to be tied to a valid UNIX uid is a design decision that was made a long way back in the history of Samba development. It is unlikely that this decision will be reversed of changed during the remaining life of the Samba-3.x series.
The resolution of a UID from the Windows SID is achieved within Samba through a mechanism that must refer back to the host operating system on which Samba is running. The Name Service Switcher (NSS) is the preferred mechanism that shields applications (like Samba) from the need to know everything about every host OS it runs on.
Samba asks the host OS to provide a UID via the “passwd”, “shadow” and “group” facilities in the NSS control (configuration) file. The best tool for achieving this is left up to the UNIX administrator to determine. It is not imposed by Samba. Samba provides winbindd together with its support libraries as one method. It is possible to do this via LDAP - and for that Samba provides the appropriate hooks so that all account entities can be located in an LDAP directory.
For many the weapon of choice is to use the PADL nss_ldap utility. This utility must be configured so that computer accounts can be resolved to a POSIX/UNIX account UID. That is fundamentally an LDAP design question. The information provided on the Samba list and in the documentation is directed at providing working examples only. The design of an LDAP directory is a complex subject that is beyond the scope of this documentation.
Samba provides two tools for management of user and machine accounts. These tools are called smbpasswd and pdbedit.
The smbpasswd utility is similar to the passwd or yppasswd programs. It maintains the two 32 byte password fields in the passdb backend.
smbpasswd works in a client-server mode where it contacts the local smbd to change the user's password on its behalf. This has enormous benefits.
smbpasswd has the capability to change passwords on Windows NT servers (this only works when the request is sent to the NT Primary Domain Controller if changing an NT Domain user's password).
add user or machine accounts.
delete user or machine accounts.
enable user or machine accounts.
disable user or machine accounts.
set to NULL user passwords.
manage interdomain trust accounts.
To run smbpasswd as a normal user just type:
$smbpasswdOld SMB password:secret
For secret, type old value here or press return if
there is no old password.
New SMB Password:new secretRepeat New SMB Password:new secret
If the old value does not match the current value stored for that user, or the two new values do not match each other, then the password will not be changed.
When invoked by an ordinary user, the command will only allow the user to change his or her own SMB password.
When run by root, smbpasswd may take an optional argument specifying the user name whose SMB password you wish to change. When run as root, smbpasswd does not prompt for or check the old password value, thus allowing root to set passwords for users who have forgotten their passwords.
smbpasswd is designed to work in the way familiar to UNIX users who use the passwd or yppasswd commands. While designed for administrative use, this tool provides essential User Level password change capabilities.
For more details on using smbpasswd, refer to the man page (the definitive reference).
pdbedit is a tool that can be used only by root. It is used to manage the passdb backend. pdbedit can be used to:
add, remove or modify user accounts.
list user accounts.
migrate user accounts.
The pdbedit tool is the only one that can manage the account security and policy settings. It is capable of all operations that smbpasswd can do as well as a super set of them.
One particularly important purpose of the pdbedit is to allow the migration of account information from one passdb backend to another. See the XML password backend section of this chapter.
The following is an example of the user account information that is stored in a tdbsam password backend. This listing was produced by running:
$pdbedit -Lv metUNIX username: met NT username: Account Flags: [UX ] User SID: S-1-5-21-1449123459-1407424037-3116680435-2004 Primary Group SID: S-1-5-21-1449123459-1407424037-3116680435-1201 Full Name: Melissa E Terpstra Home Directory: \\frodo\met\Win9Profile HomeDir Drive: H: Logon Script: scripts\logon.bat Profile Path: \\frodo\Profiles\met Domain: MIDEARTH Account desc: Workstations: melbelle Munged dial: Logon time: 0 Logoff time: Mon, 18 Jan 2038 20:14:07 GMT Kickoff time: Mon, 18 Jan 2038 20:14:07 GMT Password last set: Sat, 14 Dec 2002 14:37:03 GMT Password can change: Sat, 14 Dec 2002 14:37:03 GMT Password must change: Mon, 18 Jan 2038 20:14:07 GMT
The pdbedit tool allows migration of authentication (account)
databases from one backend to another. For example: To migrate accounts from an
old smbpasswd database to a tdbsam
backend:
Samba offers the greatest flexibility in backend account database design of any SMB/CIFS server technology available today. The flexibility is immediately obvious as one begins to explore this capability.
It is possible to specify not only multiple different password backends, but even multiple backends of the same type. For example, to use two different tdbsam databases:
passdb backend = tdbsam:/etc/samba/passdb.tdb tdbsam:/etc/samba/old-passdb.tdb |
Older versions of Samba retrieved user information from the UNIX user database
and eventually some other fields from the file /etc/samba/smbpasswd
or /etc/smbpasswd. When password encryption is disabled, no
SMB specific data is stored at all. Instead all operations are conducted via the way
that the Samba host OS will access its /etc/passwd database.
Linux systems For example, all operations are done via PAM.
Traditionally, when configuring encrypt passwords = yes in Samba's smb.conf file, user account
information such as username, LM/NT password hashes, password change times, and account
flags have been stored in the smbpasswd(5) file. There are several
disadvantages to this approach for sites with large numbers of users (counted
in the thousands).
The first problem is that all lookups must be performed sequentially. Given that there are approximately two lookups per domain logon (one for a normal session connection such as when mapping a network drive or printer), this is a performance bottleneck for large sites. What is needed is an indexed approach such as used in databases.
The second problem is that administrators who desire to replicate a smbpasswd file to more than one Samba server were left to use external tools such as rsync(1) and ssh(1) and wrote custom, in-house scripts.
Finally, the amount of information that is stored in an smbpasswd entry leaves no room for additional attributes such as a home directory, password expiration time, or even a Relative Identifier (RID).
As a result of these deficiencies, a more robust means of storing user attributes used by smbd was developed. The API which defines access to user accounts is commonly referred to as the samdb interface (previously this was called the passdb API, and is still so named in the Samba CVS trees).
Samba provides an enhanced set of passdb backends that overcome the deficiencies of the smbpasswd plain text database. These are tdbsam, ldapsam and xmlsam. Of these, ldapsam will be of most interest to large corporate or enterprise sites.
Samba can store user and machine account data in a “TDB” (Trivial Database). Using this backend does not require any additional configuration. This backend is recommended for new installations that do not require LDAP.
As a general guide, the Samba Team does not recommend using the tdbsam backend for sites that have 250 or more users. Additionally, tdbsam is not capable of scaling for use in sites that require PDB/BDC implementations that require replication of the account database. Clearly, for reason of scalability, the use of ldapsam should be encouraged.
The recommendation of a 250 user limit is purely based on the notion that this would generally involve a site that has routed networks, possibly spread across more than one physical location. The Samba Team has not at this time established the performance based scalability limits of the tdbsam architecture.
There are a few points to stress that the ldapsam does not provide. The LDAP support referred to in this documentation does not include:
A means of retrieving user account information from an Windows 200x Active Directory server.
A means of replacing /etc/passwd.
The second item can be accomplished by using LDAP NSS and PAM modules. LGPL versions of these libraries can be obtained from PADL Software. More information about the configuration of these packages may be found at LDAP, System Administration; Gerald Carter by O'Reilly; Chapter 6: Replacing NIS."
This document describes how to use an LDAP directory for storing Samba user account information traditionally stored in the smbpasswd(5) file. It is assumed that the reader already has a basic understanding of LDAP concepts and has a working directory server already installed. For more information on LDAP architectures and directories, please refer to the following sites:
Two additional Samba resources which may prove to be helpful are:
The Samba-PDC-LDAP-HOWTO maintained by Ignacio Coupeau.
The NT migration scripts from IDEALX that are geared to manage users and group in such a Samba-LDAP Domain Controller configuration.
The LDAP ldapsam code has been developed and tested using the OpenLDAP 2.0 and 2.1 server and client libraries. The same code should work with Netscape's Directory Server and client SDK. However, there are bound to be compile errors and bugs. These should not be hard to fix. Please submit fixes via the process outlined in Reporting Bugs chapter.
Samba-3.0 includes the necessary schema file for OpenLDAP 2.0 in
examples/LDAP/samba.schema. The sambaSamAccount ObjectClass is given here:
ObjectClass (1.3.6.1.4.1.7165.2.2.6 NAME 'sambaSamAccount' SUP top AUXILIARY
DESC 'Samba-3.0 Auxiliary SAM Account'
MUST ( uid $ sambaSID )
MAY ( cn $ sambaLMPassword $ sambaNTPassword $ sambaPwdLastSet $
sambaLogonTime $ sambaLogoffTime $ sambaKickoffTime $
sambaPwdCanChange $ sambaPwdMustChange $ sambaAcctFlags $
displayName $ sambaHomePath $ sambaHomeDrive $ sambaLogonScript $
sambaProfilePath $ description $ sambaUserWorkstations $
sambaPrimaryGroupSID $ sambaDomainName ))
The samba.schema file has been formatted for OpenLDAP 2.0/2.1.
The Samba Team owns the OID space used by the above schema and recommends its use.
If you translate the schema to be used with Netscape DS, please submit the modified
schema file as a patch to jerry@samba.org.
Just as the smbpasswd file is meant to store information that provides information additional to a
user's /etc/passwd entry, so is the sambaSamAccount object
meant to supplement the UNIX user account information. A sambaSamAccount is a
AUXILIARY ObjectClass so it can be used to augment existing
user account information in the LDAP directory, thus providing information needed
for Samba account handling. However, there are several fields (e.g., uid) that overlap
with the posixAccount ObjectClass outlined in RFC2307. This is by design.
In order to store all user account information (UNIX and Samba) in the directory, it is necessary to use the sambaSamAccount and posixAccount ObjectClass es in combination. However, smbd will still obtain the user's UNIX account information via the standard C library calls (e.g., getpwnam(), et al). This means that the Samba server must also have the LDAP NSS library installed and functioning correctly. This division of information makes it possible to store all Samba account information in LDAP, but still maintain UNIX account information in NIS while the network is transitioning to a full LDAP infrastructure.
To include support for the sambaSamAccount object in an OpenLDAP directory
server, first copy the samba.schema file to slapd's configuration directory.
The samba.schema file can be found in the directory examples/LDAP
in the Samba source distribution.
root#cp samba.schema /etc/openldap/schema/
Next, include the samba.schema file in slapd.conf.
The sambaSamAccount object contains two attributes that depend on other schema
files. The uid attribute is defined in cosine.schema and
the displayName attribute is defined in the inetorgperson.schema
file. Both of these must be included before the samba.schema file.
## /etc/openldap/slapd.conf ## schema files (core.schema is required by default) include /etc/openldap/schema/core.schema ## needed for sambaSamAccount include /etc/openldap/schema/cosine.schema include /etc/openldap/schema/inetorgperson.schema include /etc/openldap/schema/nis.schema include /etc/openldap/schema/samba.schema ....
It is recommended that you maintain some indices on some of the most useful attributes, as in the following example, to speed up searches made on sambaSamAccount objectclasses (and possibly posixAccount and posixGroup as well):
# Indices to maintain ## required by OpenLDAP index objectclass eq index cn pres,sub,eq index sn pres,sub,eq ## required to support pdb_getsampwnam index uid pres,sub,eq ## required to support pdb_getsambapwrid() index displayName pres,sub,eq ## uncomment these if you are storing posixAccount and ## posixGroup entries in the directory as well ##index uidNumber eq ##index gidNumber eq ##index memberUid eq index sambaSID eq index sambaPrimaryGroupSID eq index sambaDomainName eq index default sub
Create the new index by executing:
root# ./sbin/slapindex -f slapd.conf
Remember to restart slapd after making these changes:
root#/etc/init.d/slapd restart
Before you can add accounts to the LDAP database you must create the account containers that they will be stored in. The following LDIF file should be modified to match your needs (DNS entries, and so on):
# Organization for Samba Base
dn: dc=quenya,dc=org
objectclass: dcObject
objectclass: organization
dc: quenya
o: Quenya Org Network
description: The Samba-3 Network LDAP Example
# Organizational Role for Directory Management
dn: cn=Manager,dc=quenya,dc=org
objectclass: organizationalRole
cn: Manager
description: Directory Manager
# Setting up container for users
dn: ou=People,dc=quenya,dc=org
objectclass: top
objectclass: organizationalUnit
ou: People
# Setting up admin handle for People OU
dn: cn=admin,ou=People,dc=quenya,dc=org
cn: admin
objectclass: top
objectclass: organizationalRole
objectclass: simpleSecurityObject
userPassword: {SSHA}c3ZM9tBaBo9autm1dL3waDS21+JSfQVz
# Setting up container for groups
dn: ou=Groups,dc=quenya,dc=org
objectclass: top
objectclass: organizationalUnit
ou: Groups
# Setting up admin handle for Groups OU
dn: cn=admin,ou=Groups,dc=quenya,dc=org
cn: admin
objectclass: top
objectclass: organizationalRole
objectclass: simpleSecurityObject
userPassword: {SSHA}c3ZM9tBaBo9autm1dL3waDS21+JSfQVz
# Setting up container for computers
dn: ou=Computers,dc=quenya,dc=org
objectclass: top
objectclass: organizationalUnit
ou: Computers
# Setting up admin handle for Computers OU
dn: cn=admin,ou=Computers,dc=quenya,dc=org
cn: admin
objectclass: top
objectclass: organizationalRole
objectclass: simpleSecurityObject
userPassword: {SSHA}c3ZM9tBaBo9autm1dL3waDS21+JSfQVz
The userPassword shown above should be generated using slappasswd.
The following command will then load the contents of the LDIF file into the LDAP database.
$slapadd -v -l initldap.dif
Do not forget to secure your LDAP server with an adequate access control list as well as an admin password.
Note
Before Samba can access the LDAP server you need to store the LDAP admin password
into the Samba-3 secrets.tdb database by:
root#smbpasswd -wsecret
The following parameters are available in smb.conf only if your version of Samba was built with LDAP support. Samba automatically builds with LDAP support if the LDAP libraries are found.
LDAP related smb.conf options: passdb backend = ldapsam:url, ldap admin dn, ldap delete dn, ldap filter, ldap group suffix, ldap idmap suffix, ldap machine suffix, ldap passwd sync, ldap ssl, ldap suffix, ldap user suffix,
These are described in the smb.conf man
page and so will not be repeated here. However, a sample smb.conf file for
use with an LDAP directory could appear as shown below.
Example 10.2. Configuration with LDAP
As user accounts are managed through the sambaSamAccount objectclass, you should modify your existing administration tools to deal with sambaSamAccount attributes.
Machine accounts are managed with the sambaSamAccount objectclass, just
like users accounts. However, it is up to you to store those accounts
in a different tree of your LDAP namespace. You should use
“ou=Groups,dc=quenya,dc=org” to store groups and
“ou=People,dc=quenya,dc=org” to store users. Just configure your
NSS and PAM accordingly (usually, in the /etc/openldap/sldap.conf
configuration file).
In Samba-3, the group management system is based on POSIX
groups. This means that Samba makes use of the posixGroup objectclass.
For now, there is no NT-like group system management (global and local
groups). Samba-3 knows only about Domain Groups
and, unlike MS Windows 2000 and Active Directory, Samba-3 does not
support nested groups.
There are two important points to remember when discussing the security of sambaSamAccount entries in the directory.
Never retrieve the SambaLMPassword or SambaNTPassword attribute values over an unencrypted LDAP session.
Never allow non-admin users to view the SambaLMPassword or SambaNTPassword attribute values.
These password hashes are clear-text equivalents and can be used to impersonate the user without deriving the original clear-text strings. For more information on the details of LM/NT password hashes, refer to the Account Information Database section of this chapter.
To remedy the first security issue, the ldap ssl smb.conf parameter defaults
to require an encrypted session (ldap ssl = on) using
the default port of 636
when contacting the directory server. When using an OpenLDAP server, it
is possible to use the StartTLS LDAP extended operation in the place of
LDAPS. In either case, you are strongly discouraged to disable this security
(ldap ssl = off).
Note that the LDAPS protocol is deprecated in favor of the LDAPv3 StartTLS extended operation. However, the OpenLDAP library still provides support for the older method of securing communication between clients and servers.
The second security precaution is to prevent non-administrative users from
harvesting password hashes from the directory. This can be done using the
following ACL in slapd.conf:
## allow the "ldap admin dn" access, but deny everyone else
access to attrs=SambaLMPassword,SambaNTPassword
by dn="cn=Samba Admin,ou=People,dc=quenya,dc=org" write
by * none
The sambaSamAccount objectclass is composed of the attributes shown in next tables: Part A, and Part B.
Table 10.1. Attributes in the sambaSamAccount objectclass (LDAP) Part A
Table 10.2. Attributes in the sambaSamAccount objectclass (LDAP) Part B
sambaUserWorkstations | Here you can give a comma-separated list of machines on which the user is allowed to login. You may observe problems when you try to connect to an Samba Domain Member. Because Domain Members are not in this list, the Domain Controllers will reject them. Where this attribute is omitted, the default implies no restrictions. |
sambaSID | The security identifier(SID) of the user. The Windows equivalent of UNIX UIDs. |
sambaPrimaryGroupSID | The Security IDentifier (SID) of the primary group of the user. |
sambaDomainName | Domain the user is part of. |
The majority of these parameters are only used when Samba is acting as a PDC of a domain (refer to Domain Control, for details on how to configure Samba as a Primary Domain Controller). The following four attributes are only stored with the sambaSamAccount entry if the values are non-default values:
sambaHomePath
sambaLogonScript
sambaProfilePath
sambaHomeDrive
These attributes are only stored with the sambaSamAccount entry if
the values are non-default values. For example, assume MORIA has now been
configured as a PDC and that logon home = \\%L\%u was defined in
its smb.conf file. When a user named “becky” logons to the domain,
the logon home string is expanded to \\MORIA\becky.
If the smbHome attribute exists in the entry “uid=becky,ou=People,dc=samba,dc=org”,
this value is used. However, if this attribute does not exist, then the value
of the logon home parameter is used in its place. Samba
will only write the attribute value to the directory entry if the value is
something other than the default (e.g., \\MOBY\becky).
The following is a working LDIF that demonstrates the use of the SambaSamAccount objectclass:
dn: uid=guest2, ou=People,dc=quenya,dc=org sambaLMPassword: 878D8014606CDA29677A44EFA1353FC7 sambaPwdMustChange: 2147483647 sambaPrimaryGroupSID: S-1-5-21-2447931902-1787058256-3961074038-513 sambaNTPassword: 552902031BEDE9EFAAD3B435B51404EE sambaPwdLastSet: 1010179124 sambaLogonTime: 0 objectClass: sambaSamAccount uid: guest2 sambaKickoffTime: 2147483647 sambaAcctFlags: [UX ] sambaLogoffTime: 2147483647 sambaSID: S-1-5-21-2447931902-1787058256-3961074038-5006 sambaPwdCanChange: 0
The following is an LDIF entry for using both the sambaSamAccount and posixAccount objectclasses:
dn: uid=gcarter, ou=People,dc=quenya,dc=org
sambaLogonTime: 0
displayName: Gerald Carter
sambaLMPassword: 552902031BEDE9EFAAD3B435B51404EE
sambaPrimaryGroupSID: S-1-5-21-2447931902-1787058256-3961074038-1201
objectClass: posixAccount
objectClass: sambaSamAccount
sambaAcctFlags: [UX ]
userPassword: {crypt}BpM2ej8Rkzogo
uid: gcarter
uidNumber: 9000
cn: Gerald Carter
loginShell: /bin/bash
logoffTime: 2147483647
gidNumber: 100
sambaKickoffTime: 2147483647
sambaPwdLastSet: 1010179230
sambaSID: S-1-5-21-2447931902-1787058256-3961074038-5004
homeDirectory: /home/moria/gcarter
sambaPwdCanChange: 0
sambaPwdMustChange: 2147483647
sambaNTPassword: 878D8014606CDA29677A44EFA1353FC7
Samba-3 and later can update the non-samba (LDAP) password stored with an account. When using pam_ldap, this allows changing both UNIX and Windows passwords at once.
The ldap passwd sync options can have the values shown in the next table.
Table 10.3. Possible ldap passwd sync values
| Value | Description |
|---|---|
| yes | When the user changes his password, update
|
| no | Only update |
| only | Only update the LDAP password and let the LDAP server worry about the other fields. This option is only available on some LDAP servers. Only when the LDAP server supports LDAP_EXOP_X_MODIFY_PASSWD. |
More information can be found in the smb.conf man page.
Every so often someone will come along with a great new idea. Storing user accounts in a SQL backend is one of them. Those who want to do this are in the best position to know what the specific benefits are to them. This may sound like a cop-out, but in truth we cannot attempt to document every little detail why certain things of marginal utility to the bulk of Samba users might make sense to the rest. In any case, the following instructions should help the determined SQL user to implement a working system.
You can set up your own table and specify the field names to pdb_mysql (see below
for the column names) or use the default table. The file examples/pdb/mysql/mysql.dump
contains the correct queries to create the required tables. Use the command:
$mysql -uusername-hhostname-ppassword\databasename</path/to/samba/examples/pdb/mysql/mysql.dump
This plug-in lacks some good documentation, but here is some brief information. Add the following to the
passdb backend variable in your smb.conf:
passdb backend = [other-plugins] mysql:identifier [other-plugins] |
The identifier can be any string you like, as long as it does not collide with the identifiers of other plugins or other instances of pdb_mysql. If you specify multiple pdb_mysql.so entries in passdb backend, you also need to use different identifiers.
Additional options can be given through the smb.conf file in the [global] section.
Refer to the following table.
Table 10.4. Basic smb.conf options for MySQL passdb backend
| Field | Contents |
|---|---|
| mysql host | Host name, defaults to `localhost' |
| mysql password | |
| mysql user | Defaults to `samba' |
| mysql database | Defaults to `samba' |
| mysql port | Defaults to 3306 |
| table | Name of the table containing the users |
Warning
Since the password for the MySQL user is stored in the smb.conf file, you should make the smb.conf file
readable only to the user who runs Samba. This is considered a security bug and will soon be fixed.
Names of the columns are given in the next table. The default column names can be found in the example table dump.
Table 10.5. MySQL field names for MySQL passdb backend
You can put a colon (:) after the name of each column, which
should specify the column to update when updating the table. One can also specify nothing behind the colon, in which case the field data will not be updated. Setting a column name to NULL means the field should not be used.
An example configuration looks like:
Example 10.3. Example configuration for the MySQL passdb backend
I strongly discourage the use of plaintext passwords, however, you can use them.
If you would like to use plaintext passwords, set `identifier:lanman pass column' and `identifier:nt pass column' to `NULL' (without the quotes) and `identifier:plain pass column' to the name of the column containing the plaintext passwords.
If you use encrypted passwords, set the 'identifier:plain pass column' to 'NULL' (without the quotes). This is the default.
It is possible to have not all data in the database by making some `constant'.
For example, you can set `identifier:fullname column' to something like CONCAT(Firstname,' ',Surname)
Or, set `identifier:workstations column' to: NULL
See the MySQL documentation for more language constructs.
“I've installed Samba, but now I can't log on with my UNIX account! ”
Make sure your user has been added to the current Samba passdb backend. Read the section Account Management Tools for details.
A few complaints have been received from users that just moved to Samba-3. The following
smb.conf file entries were causing problems, new accounts were being added to the old
smbpasswd file, not to the tdbsam passdb.tdb file:
[global] |
| ... |
passdb backend = smbpasswd, tdbsam |
| ... |
Samba will add new accounts to the first entry in the passdb backend parameter entry. If you want to update to the tdbsam, then change the entry to:
passdb backend = tdbsam, smbpasswd |